From implementation to ongoing support, we deliver comprehensive Yardi solutions tailored to your business.
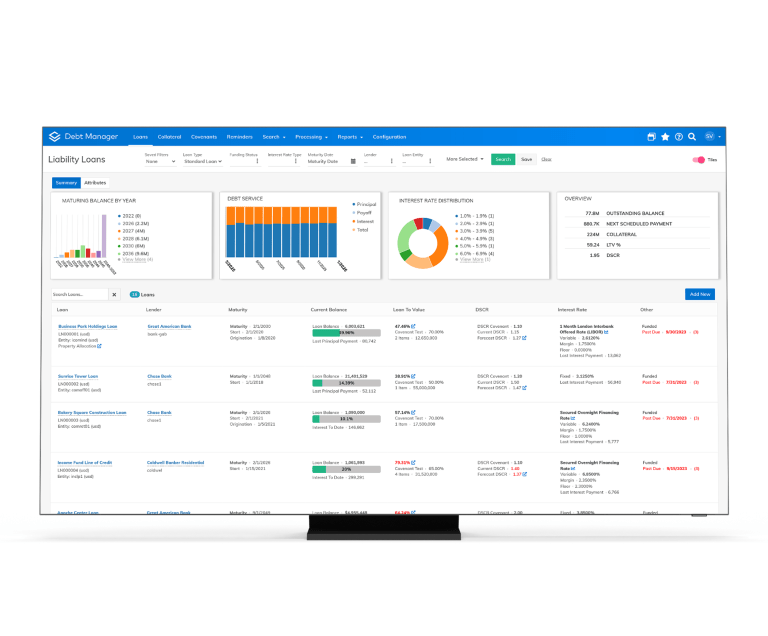
We are a specialized Yardi consulting company dedicated to helping real estate organizations unlock the full potential of their technology investments. With deep industry expertise and a client-first approach, we deliver scalable Yardi solutions that streamline operations,improve data visibility, and drive long-term growth.
Our team combines technical excellence with real estate domain knowledge to provide end-to-end services — from implementation and customization to ongoing support and optimization. We partner closely with our clients to understand their unique challenges and build solutions that create measurable business impact.
Book An Appointment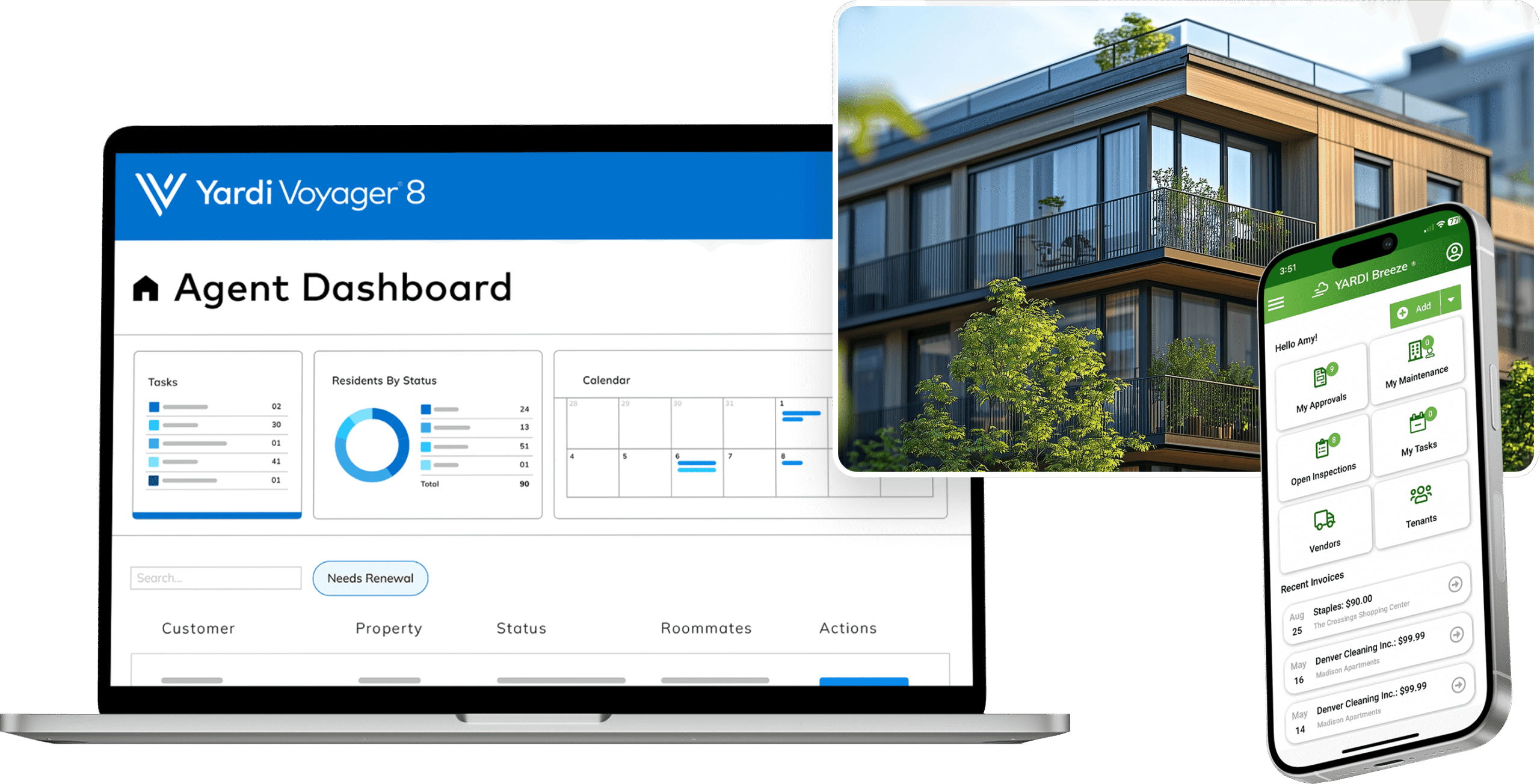
We deliver industry-focused Yardi solutions that streamline real estate operations and drive smarter, scalable growth.

Discover real success stories, measurable results, and the impact we create for our clients.
Share practical knowledge, emerging trends, and best practices to help you get more value from your real estate technology.